Group Policy WMI Filtering was introduced with Windows XP, and is a great way to add a decision on when to apply a given group policy. WMI Filters, written in WMI Query Language (WQL), allow an administrator to specify a WMI-based query to filter the application of a GPO. WMI Filtering can be very useful when users or computers are located in a relatively flat OU structure in Active Directory, for example. WMI Filters can also allow you to apply specific policies based on server roles, operating system version, network configuration, and other criteria. Windows evaluates these filters in the following order of overall Group Policy Processing:
- Policies are located in hierarchy.
- The WMI Filters are checked.
- The security settings are checked.
- A policy is either filtered or applied depending on the results of the previous checks.
Breakdown: We locate all of the policies that exist in the user or computer’s Local, Site, Domain, and OU hierarchy. We then determine if the WMI Filter (if any are defined) returns TRUE. We then verify that the user or computer has both Read and Apply group policy permissions for the GPO. Once all of that is validated, the group policy is applied.
The order of evaluation does mean that WMI Filters are less efficient than hierarchical linking, but are useful when you need to make decisions in a non-hierarchical Active Directory design. WMI Filters can be configuredusing the WMI Filters node in the Group Policy Management Console, or GPMC.MSC.

For more information, see Applying Group Policy.
Over the years, I’ve needed to use WMI Filtering pretty extensively. One very useful resource I’ve come across is GPOGuy, where you’ll find FAQs, whitepapers, videos, freeware and more. One of the most useful tools I’ve found for writing, optimizing and validating WMI Filters is the WMI Filter Validation Utility. In the interest of saving you some time and headache, here are a few WMI Filters to get you started:
All Computers and Servers
All Computers Not Domain Controllers
Application Office 2016 Installed
Execute on Friday
Execute on Monday
Execute on Saturday
Execute on Sunday
Execute on Thursday
Execute on Tuesday
Execute on Wednesday
Only ADFS Servers
Only Client OS
Only Client OS Virtual Machines
Only Desktops
Only Domain Controllers
Only Laptops
Only PDC Emulator
Only Server OS
Only Server OS Virtual Machines
Only SQL Database Servers
Only SQL Server 2016 Database Servers
Only Web Servers (IIS)
Only Windows 10
Only Windows 7
Only Windows 8
Only Windows 8.1
Only x64 Client OS
Only x64 Server OS
Only x86 Client OS
Only x86 Server OS
Right-click the links above and choose Save link as… to save the .MOF file to your computer. You can then import them by right-clicking on the WMI Filters node in the Group Policy Management Console and choosing Import.
To apply a WMI filter to a group policy:
- Click on the group policy you want to apply the filter to.
- Click on the Scope tab.
- At the bottom under the Security Filtering section, you’ll see the WMI Filtering section.
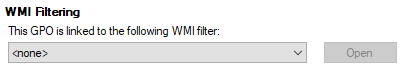
- Choose the WMI Filter that you want to apply from the dropdown and your filter will be applied to that group policy.
- Accolades
Scott is an experienced professional and recognized leader specializing in the design and implementation of enterprise virtualization, enterprise storage, server infrastructures and operations. A self-starter able to work both independently and in a team-oriented environment, Scott has a proven ability to create and automate solutions to improve productivity, reliability and performance.
Throughout his professional career, Scott has proven successes implementing technology and service improvement initiatives and has a demonstrated ability to think strategically about business, create technical definition around objectives in complex situations, develop solution strategies, motivate and mobilize resources, and deliver end-to-end technology solutions.
Scott has achieved multiple industry recognized certifications in virtualization, networking, cloud, storage, converged infrastructure, hyperconverged infrastructure and other technologies, and is honored to be a VMware vExpert in 2018-2022, and vExpert EUC 2020-2022.


Achievements
VMware vExpert EUC 2020-2022
VMware vExpert 2022
VMware vExpert 2021
VMware vExpert 2020
VMware vExpert 2019
VMware vExpert 2018
Double VCP – Data Center Virtualization & Desktop Mobility
Double VCP – Data Center Virtualization & Cloud Management
Double VCP – Data Center Virtualization & Network Virtualization
Double VCP – Network Virtualization & Desktop Mobility
Double VCP – Network Virtualization & Cloud Management
Double VCP – Cloud Management & Desktop Mobility
Dell Technologies Proven Professional Exam Developer – 2021
Certifications
VMware Certified Associate – Digital Business Transformation 2020
VMware Certified Professional – Desktop and Mobility 2020
VMware Certified Professional – Data Center Virtualization 2020
VMware Certified Professional 6 – Desktop and Mobility
VMware Certified Professional 6 – Cloud Management and Automation
VMware Certified Professional 6 – Network Virtualization
VMware Certified Professional 6 – Data Center Virtualization
VMware vSphere 6 Foundations
Dell Technologies Cloud Platform Administrator 2020
Dell Technologies Virtual Desktop Infrastructure 2019
Dell Technologies Specialist – Infrastructure Security Version 1.0
Dell Technologies Specialist – Systems Administrator, VxRail Appliance Version 2.0
Dell Technologies Specialist – Systems Administrator, VxRail Appliance Version 1.0
Dell Technologies Associate – Converged Systems and Hybrid Cloud Version 2.0
Dell Technologies and VMware Co-Skilled Associate – Converged Systems and Hybrid Cloud
IBM Enterprise Design Thinking Practitioner
IBM Enterprise Design Thinking Co-Creator
SolarWinds Certified Professional